Digital advertising fraud security firm White Opsreleased a report Tuesday detailing the exploits of “Methbot,” a new variation on the botnet. The firm says Russian cybercriminals have used Methbot to siphon off $3 to $5 million in video ad revenue from premium publishers every day.
The operation targeted high value video advertising inventory, including inventory sold through private marketplaces, by spoofing more than 6,000 premium publisher domains and creating fake pages on which it could run real ads from real advertisers. White Ops is releasing a list of 250,267 URLs that were generated by Methbot across 6,111 publisher domains. Some example fake pages from the report:
- http://ibtimes.co.uk/video
- http://vogue.com/video
- http://economist.com/video
- http://espn.com/video
- http://www.cbssports.com/CBS_Air_Force_Falcons_Fall_Gear
- http://fortune.com/2016/09/28/department-stores-closings/
- http://foxnews.com/video
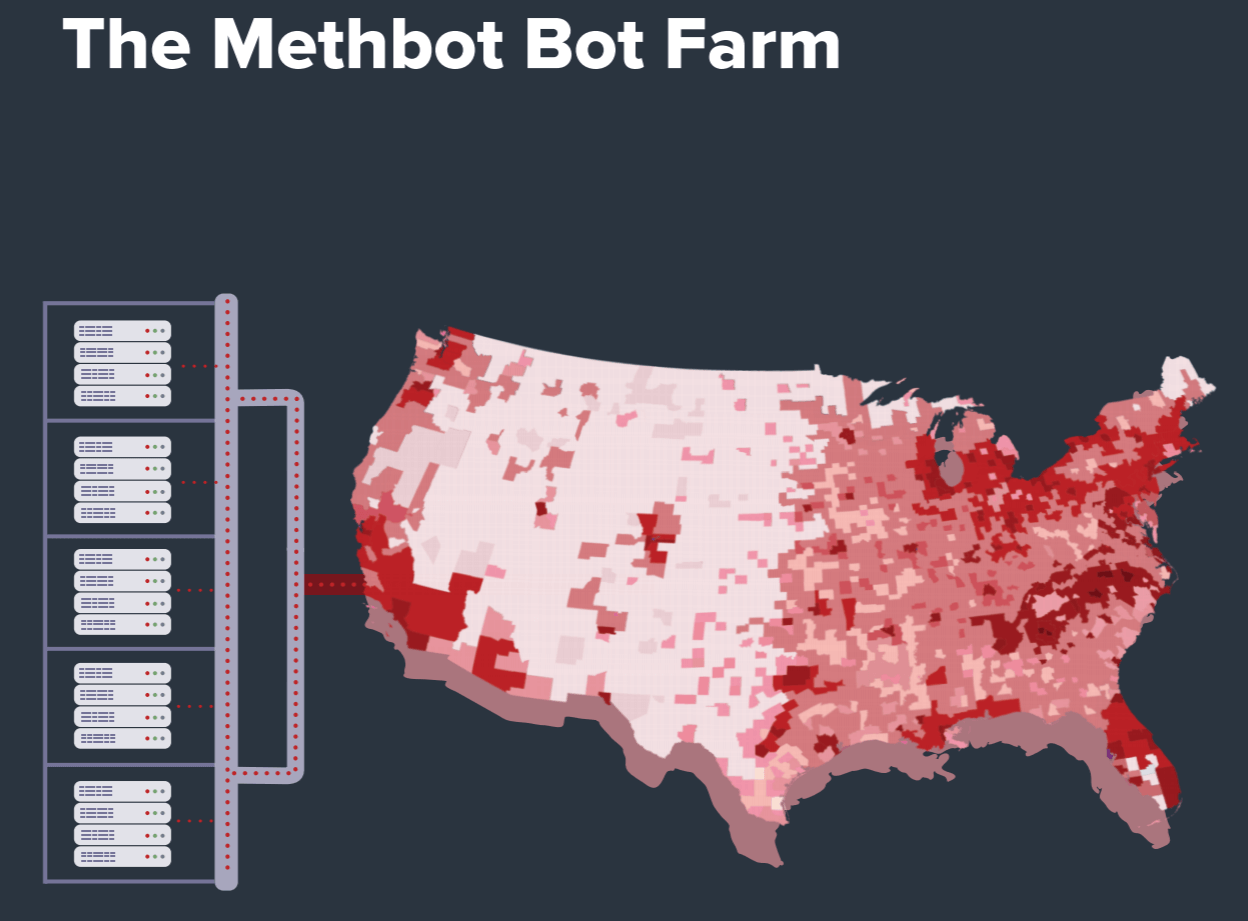
What makes Methbot unique from other major botnets is that instead of hijacking home computers at the user level, the Russian cyber criminals invested in building a network of 800 to 1,200 dedicated servers running from data servers in the US and the Netherlands. The perpetrators then obtained or leased 571,904 real IP addresses. The real IP addresses mask the fake ad calls by making them appear to come from legitimate residential Internet Service Providers such as Verizon, Comcast, and Spectrum.
IPv4 Market Group estimated the IP addresses alone currently are valued at over $4 million.
Using sophisticated anti-fraud detection methods and faking human activity (in addition to faking cursor movements and clicks to mimic human activity, Methbot forges fake social network login information to make it appear that a user is logged in when an impression occurs), White Ops believes Methbot is by far the biggest ad fraud scam to affect digital advertising.
White Ops worked with AD/FIN, a programmatic media intelligence company, to get a sense of the economic impact of Methbot. White Ops estimates the botnet has been generating between 200 to 300 million video ad impressions daily since early October. AD/FIN determined the CPMs on the ad impressions targeted ranged from $3.27 to $36.72, averaging to $13.04. That works out to $3 to $5 million in stolen ad revenue each day.
For comparison, the ZeroAccess botnet was estimated to take in $900,000 per day and the Chameleon botnet, $200,000 per day.
White Ops says it first noticed what appears to be the initial seed of Methbot in September 2015. The botnet generated little activity among White Ops clients until it rapidlydeveloped into what the security firm dubbed Methbot for the references to “meth” in its code in October of this year.
White Ops has partnered with The Trustworthy Accountability Group (TAG)
tagtoday.net, a consortium of industry associations, to help disseminate information and data including the list of known IP addresses used by Methbot and falsified domains and URLs to help the industry shut down Methbot’s operation.